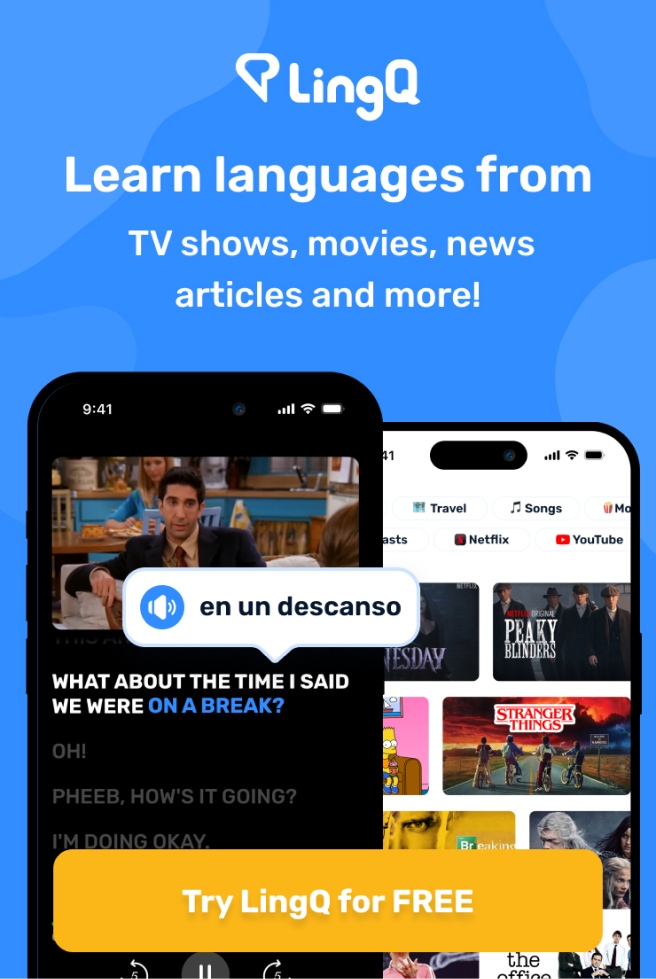
來自LingQ圖書館的示例
重覆密碼
- asymmetric warfare
- asymmetric relationships
- integrate asymmetric capabilities
- asymmetric capabilities
- asymmetric information
- Asymmetric shock
- asymmetric encryption
- utilize asymmetric encryption
- asymmetric value function
- asymmetric arms